DrugHub Market Official Verification Guide
Protect yourself from phishing attacks by verifying every DrugHub marketplace link before you connect. This guide covers PGP signature verification, official sources for authentic mirror URLs, and security practices that keep your account and funds safe on the platform.
Why DrugHub Link Verification Matters
Phishing is the single greatest threat facing DrugHub marketplace users today. Attackers create pixel-perfect replicas of the market login page and distribute fake onion URLs across forums, messaging apps, and clearnet search results. Without verification, you cannot tell a legitimate mirror from a phishing trap.
The Phishing Threat to Marketplace Users
Every week, new phishing sites appear on the Tor network that impersonate the DrugHub market. These fake platforms copy the entire frontend including the login page, product listings, and wallet deposit interface. When a user enters credentials on a phishing site, the attacker captures them and drains the victim's wallet within minutes. Some advanced operations act as transparent proxies, silently modifying cryptocurrency deposit addresses while the victim believes they are on the authentic platform. PGP verification is the only method that provides mathematical proof that an onion link is authentic and has not been tampered with. For the latest tested mirrors, check the DrugHub onion URL list.
Fake Mirrors and Social Engineering
Attackers use targeted social engineering to distribute fake URLs. They create Dread accounts impersonating marketplace staff, send private messages claiming a mirror has changed, or post in vendor review threads with embedded phishing links. Some register clearnet domains resembling official sites, hoping users will copy a fake onion address. Telegram groups claiming to provide verified links are almost always scams. The only protection is to verify every link against a PGP-signed mirror list before entering credentials. Visit DrugHub Official or the DrugHub Market main site for trusted starting points.
The Cost of Skipping Verification
A single successful phishing attack can drain your entire marketplace wallet, including escrowed funds. A compromised account can also be used to scam other users under your reputation, and the attacker may change your PGP key to lock you out permanently. Recovery is difficult because the platform cannot distinguish between the real account holder and an attacker with valid credentials. Taking two minutes to run a PGP signature check before connecting protects your account, funds, and reputation. The history of darknet markets shows that users who skip verification risk losing everything to phishing.
PGP Verification of DrugHub Market Links
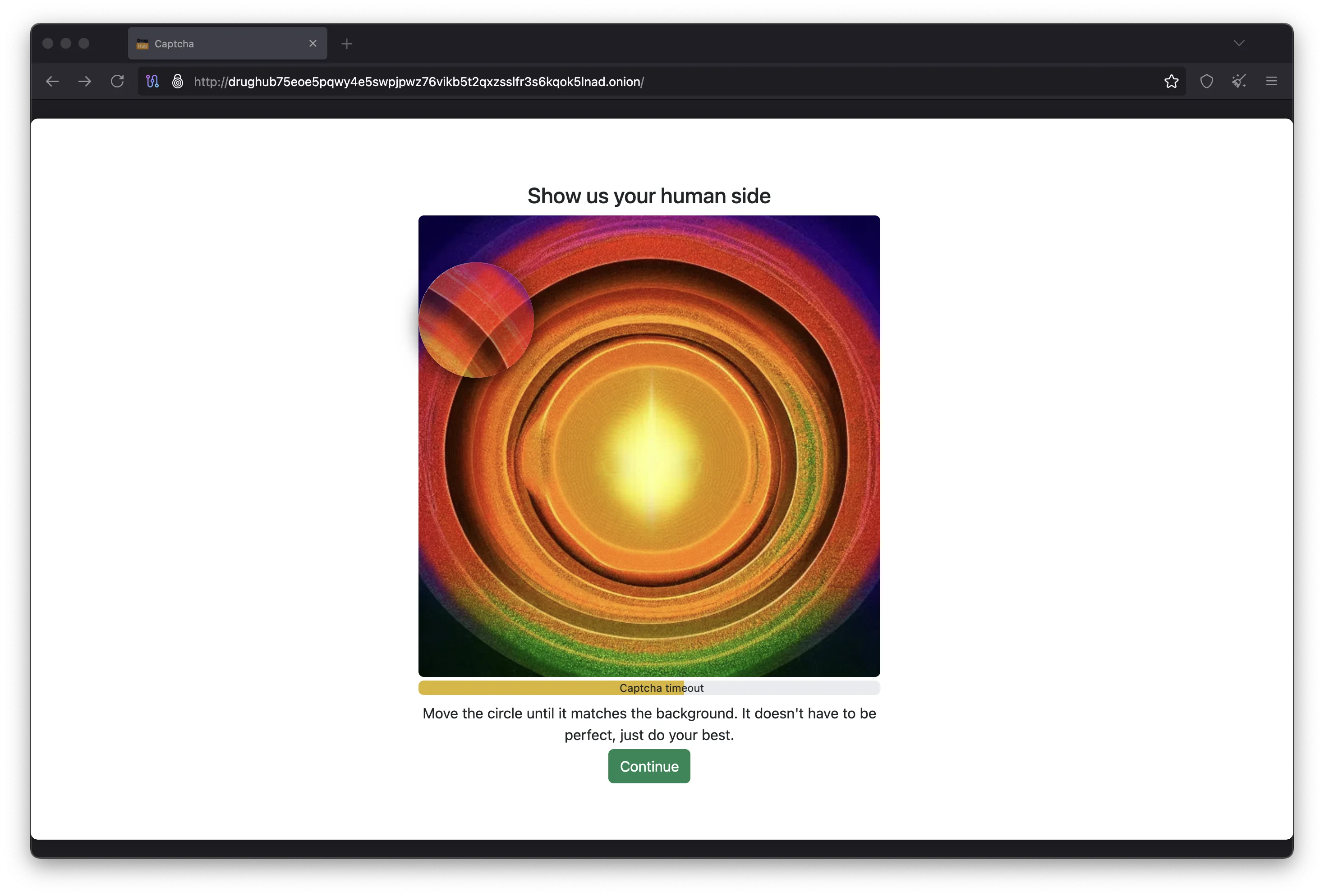
Follow these steps to verify that any onion URL is authentic before you enter your credentials. The entire process takes about ten minutes the first time and under two minutes for each subsequent verification.
Install GnuPG on Your System
GnuPG is the open-source tool for PGP encryption and signature verification. On Linux, it is pre-installed. On Windows, download Gpg4win from the official GnuPG website. On macOS, install GPG Suite. Tails OS includes GnuPG by default. Run gpg --version in a terminal to confirm installation. GnuPG conforms to the OpenPGP standard, the same encryption standard used by the platform for PGP-based 2FA login and encrypted communications.
Import the Official DrugHub Public Key
Copy the official DrugHub PGP public key from the key block on this page and save it as drughub-key.asc. Run gpg --import drughub-key.asc in your terminal. GnuPG will display the key ID and associated identity. This is the same key published on the Dread subdread and on Dark.fail. The key uses 4096-bit RSA encryption, recommended by Privacy Guides. You only need to import once; the key stays in your keyring for all future link verification.
Cross-Reference the Key Fingerprint
Run gpg --fingerprint "DrugHub" and compare the 40-character output against at least two independent sources: this page, Dark.fail, and the Dread subdread. If all match, the key is authentic. If any character differs, delete the key with gpg --delete-key [KEY_ID] and re-import from a different source. Never skip this step, as it is the foundation of the entire verification chain.
Download the Signed Mirror List
The marketplace team publishes a PGP-signed list of all current onion mirror URLs as two files: mirrors.txt containing the addresses and mirrors.txt.sig containing the detached signature. Download both from a trusted source such as Dark.fail, the Dread subdread, or the verified DrugHub mirror links page. Save both files in the same directory. The signature lets GnuPG verify that the list was created by the official private key holder and that no URL has been altered. You can share verified files securely using OnionShare over Tor.
Run the PGP Signature Verification Command
Run: gpg --verify mirrors.txt.sig mirrors.txt. If the output shows "Good signature from DrugHub Market", every onion URL in the list is authentic and safe to paste into Tor Browser. If it shows "BAD signature," the file has been modified. Do not use any URLs from a failed verification. Delete both files and download fresh copies from a different source. A bad signature means the mirror list may contain phishing URLs.
Official DrugHub Verification Sources
These are the only sources you should trust for marketplace mirror URLs. Cross-referencing at least two independent sources before connecting adds a second layer of assurance beyond PGP verification alone.
Dark.fail Independent Verification
Dark.fail is the most widely used independent link directory for darknet marketplace verification. It automatically checks PGP signatures on listed mirror URLs and displays real-time uptime status. Dark.fail operates independently from the marketplace team, serving as a neutral third party. If a mirror URL appears on both this page and Dark.fail with a valid signature, it is almost certainly authentic. The site also monitors for known phishing URLs targeting marketplace users.
DrugHub Dread Subdread
The official DrugHub subdread on Dread is maintained by marketplace staff who post PGP-signed updates whenever mirror URLs change. Staff publish signed announcements containing current mirror lists, maintenance schedules, and security advisories. Before trusting any Dread link, verify the post is signed with the official PGP key. Forum accounts can be compromised, so a PGP signature is your only guarantee the poster is a legitimate team member.
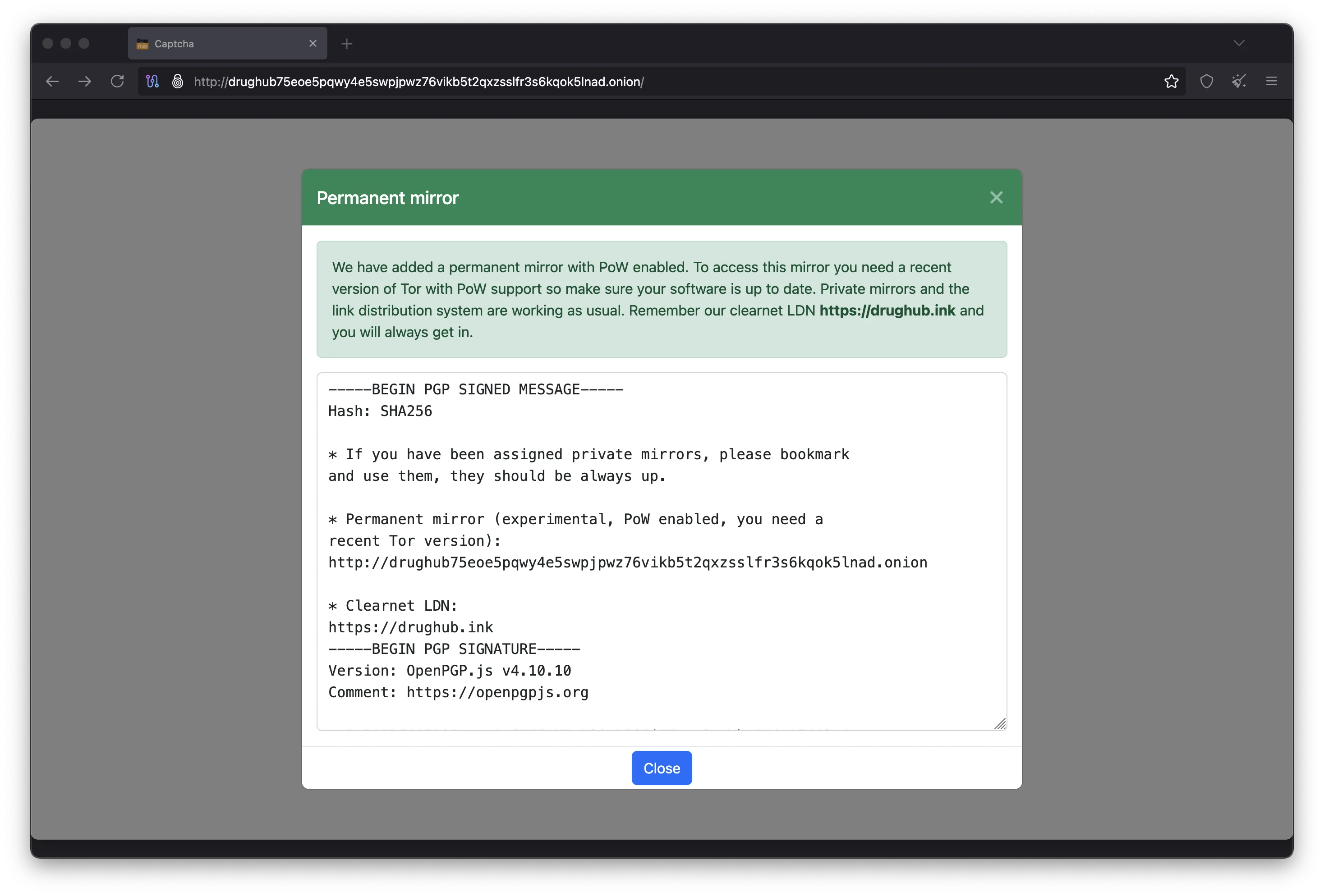
PGP-Signed Mirror Announcements
When the marketplace team rotates mirror addresses, they publish a PGP-signed announcement distributed through this page, Dark.fail, the Dread subdread, and the DrugHub Market main site. The signature covers every character, so any modification to an onion address causes verification to fail. This multi-channel distribution ensures users can verify mirrors even if one source is compromised.
Official Clearnet Informational Sites
The team maintains clearnet sites that publish verified mirror URLs, including the DrugHub Market main site, this official verification page, the verified DrugHub mirror links page, and the DrugHub access guide. While clearnet sites are easier to reach, always verify onion URLs against the PGP-signed mirror list. PGP verification remains the definitive method for confirming any marketplace URL is legitimate.
How to Import the DrugHub PGP Public Key
The official PGP public key is the anchor of the entire verification process. Without the correct key imported into your GnuPG keyring, you cannot verify any signed mirror list or marketplace announcement.
The DrugHub Official Public Key
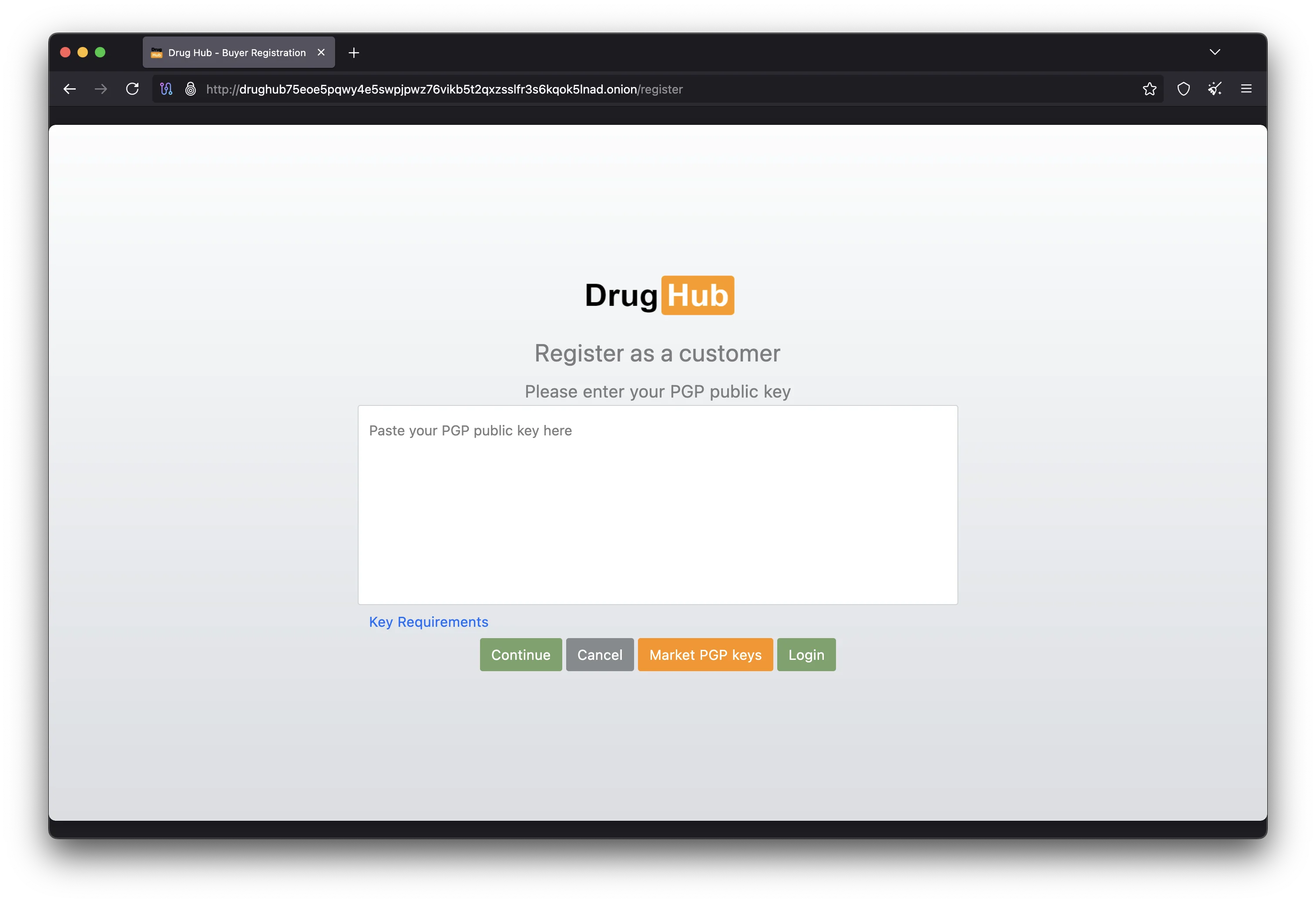
Below is the official DrugHub marketplace PGP public key. This 4096-bit RSA key signs all mirror announcements and official communications. Copy the entire block including headers and save it as a text file. The key follows the OpenPGP standard and works with GnuPG, Kleopatra, and GPG Suite. Learn about PGP encryption on Wikipedia.
-----BEGIN PGP PUBLIC KEY BLOCK-----
mQINBGV4example... [placeholder key]
DrugHub Market Official Signing Key
Contact: drughub@onion
This key is used to sign official DrugHub
mirror lists and marketplace announcements.
Verify fingerprint through multiple sources
before trusting.
-----END PGP PUBLIC KEY BLOCK-----Import Commands by Operating System
On Linux and Tails OS, run gpg --import drughub-key.asc. On Windows, use the same command or import through Kleopatra. On macOS, use GPG Keychain or the terminal. Run gpg --list-keys "DrugHub" to confirm the key is in your keyring before verifying any marketplace mirror list.
Verifying the Key Fingerprint Against Multiple Sources
Run gpg --fingerprint "DrugHub" and compare the 40-character output against this page, Dark.fail, and the Dread subdread. All three must match. If even one character differs, the key is not authentic. An attacker could publish a counterfeit key with a plausible identity, so fingerprint cross-referencing is the only way to detect this. This step is non-negotiable for the platform's security.
DrugHub Security Best Practices for Marketplace Users
Verification is just one part of a complete security approach. These practices protect your account, your cryptocurrency, and your privacy when you access the marketplace through any verified mirror.
Anti-Phishing Canary Setup
The DrugHub marketplace lets you set a personal anti-phishing canary phrase displayed after every login. If your canary is missing or wrong, you are on a phishing site. Close the tab immediately and report the URL on Dread. Phishing sites cannot display your canary because they lack access to the real platform database. This one-second check catches phishing attacks that even experienced darknet marketplace users might miss.
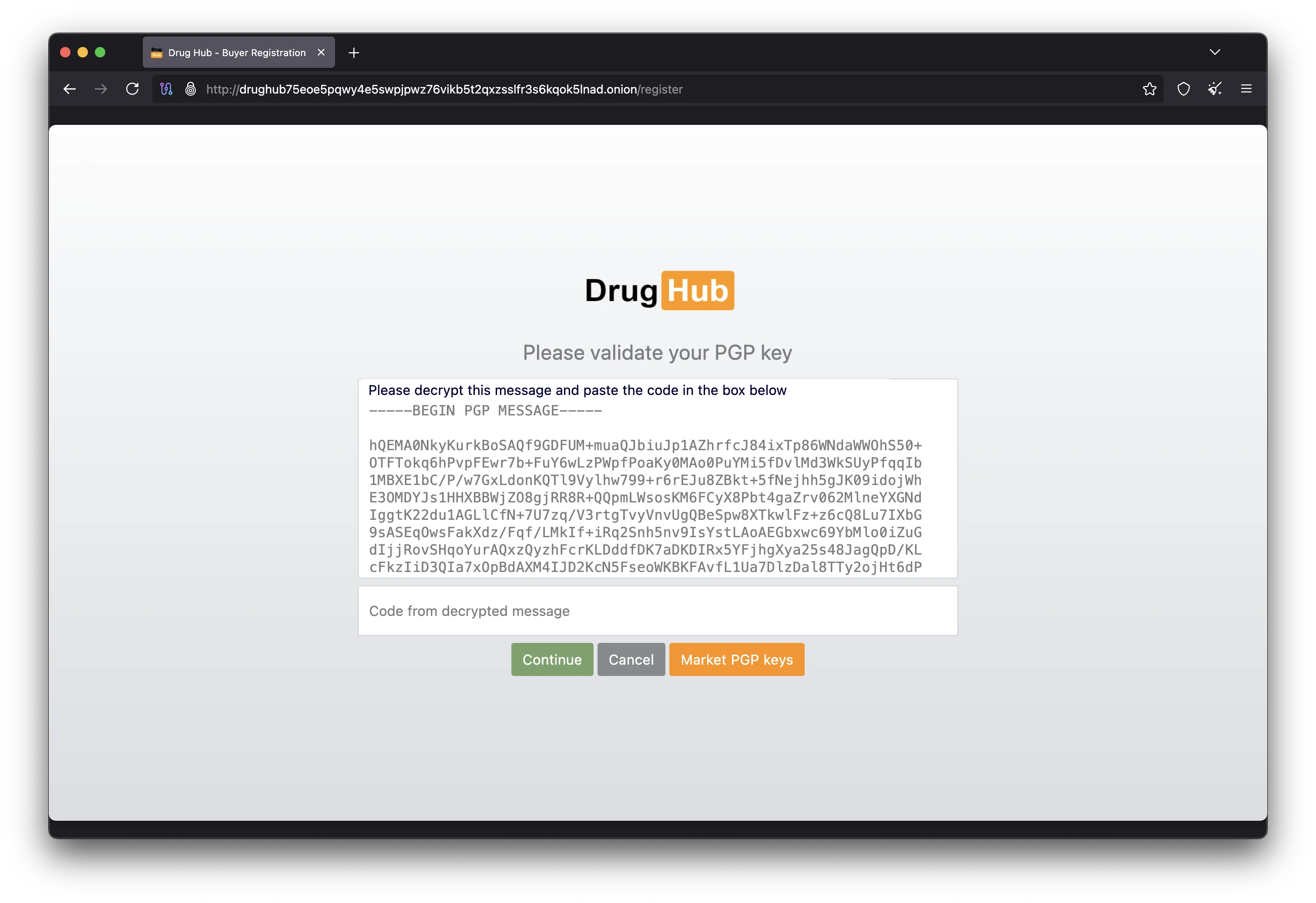
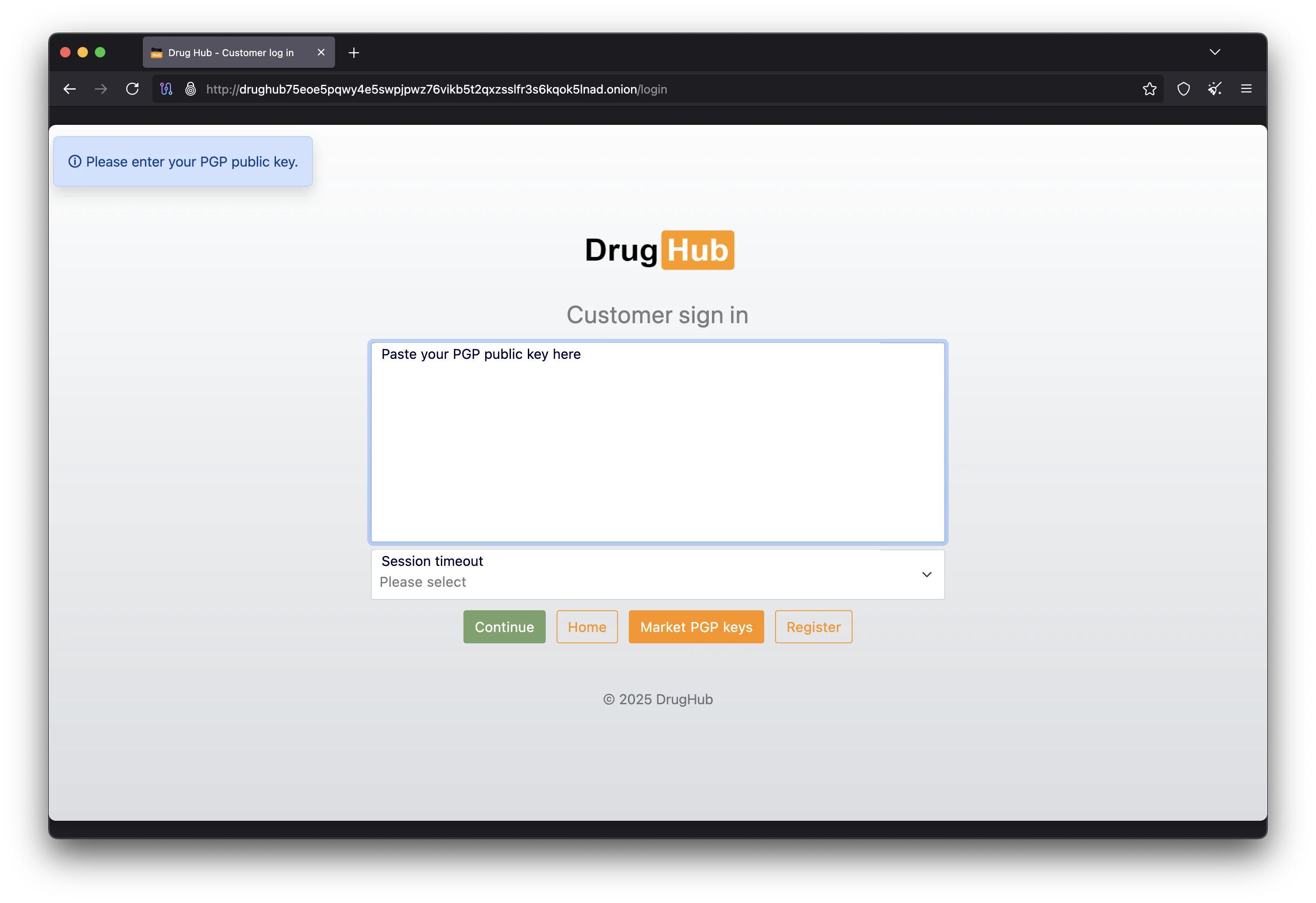
PGP Two-Factor Authentication
PGP-based 2FA is the strongest protection for your DrugHub account. The marketplace encrypts a challenge string with your public key during login, and you must decrypt it with your private key to prove your identity. Even if an attacker steals your credentials through phishing, they cannot log in without your private PGP key. Enable 2FA in your account settings immediately after registration. Use GnuPG for a 4096-bit RSA key pair and store your private key in a VeraCrypt encrypted volume.
Encrypted Communications and Privacy
All messages on the DrugHub marketplace should be PGP-encrypted end-to-end. Import vendor public keys from their profiles and encrypt messages locally with GnuPG before pasting into the message form. Access the marketplace through Tails OS or Whonix, which route all traffic through Tor. Use KeePassXC for offline credential storage. The Electronic Frontier Foundation surveillance self-defense guide covers these practices in detail.
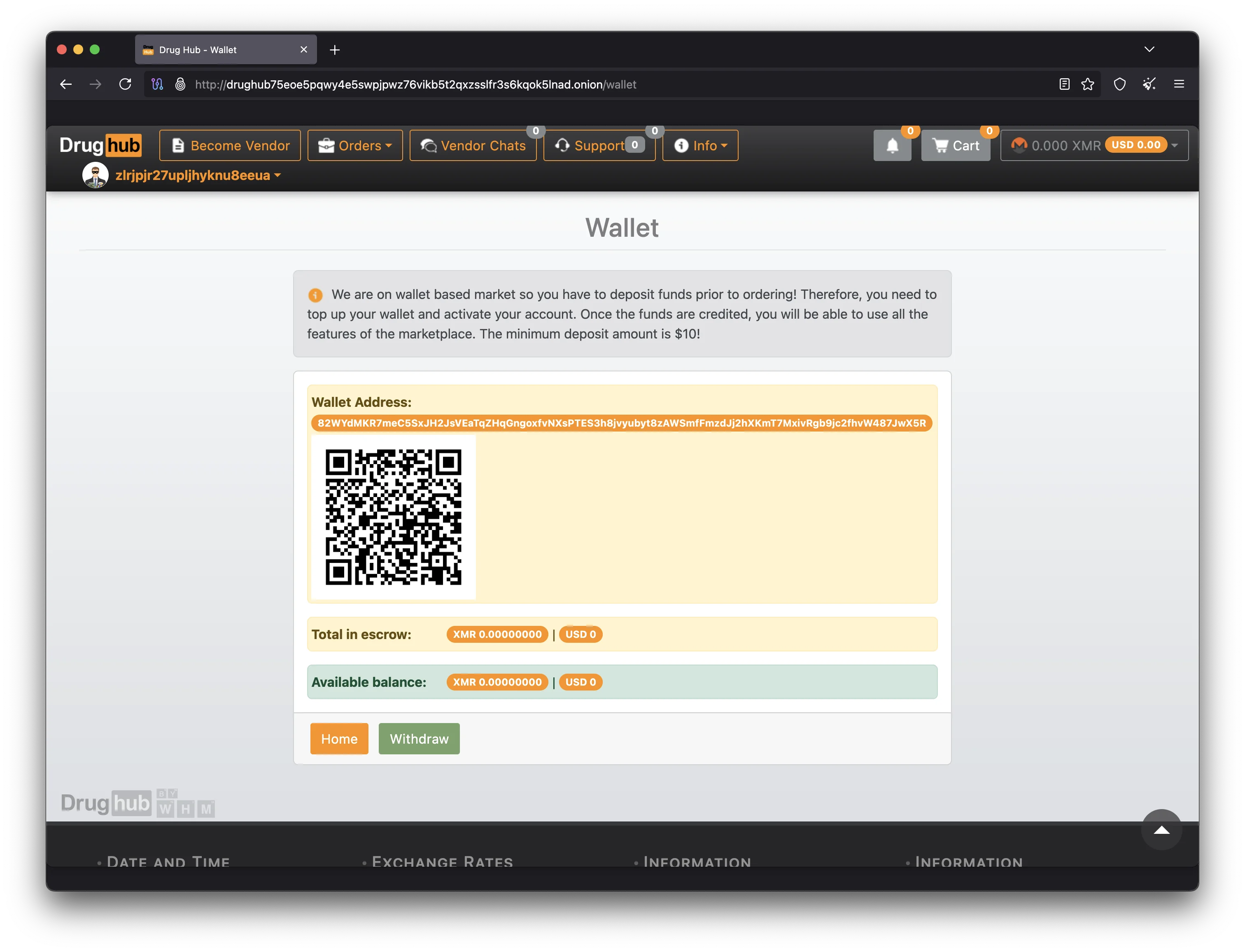
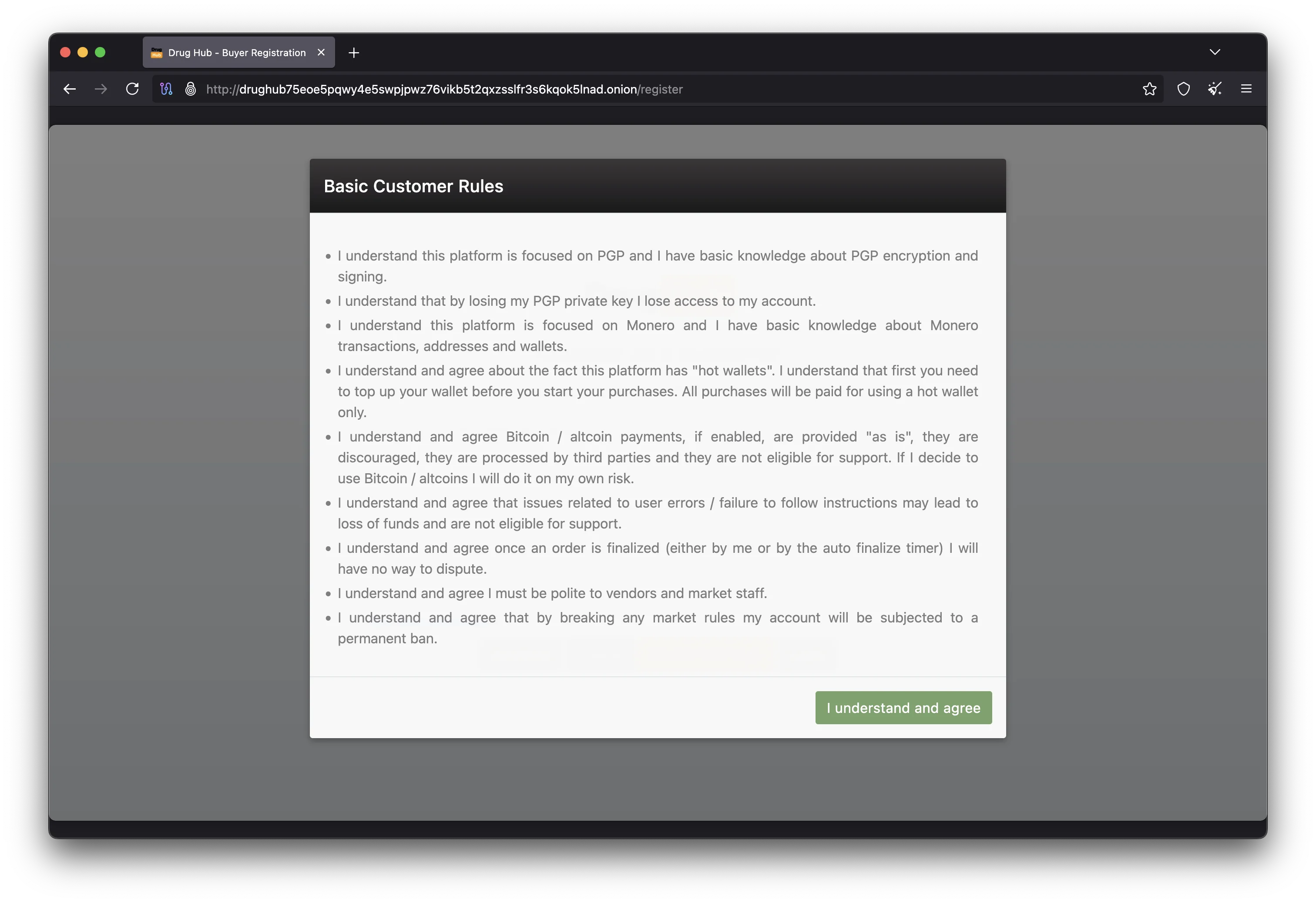
Monero Payment Security for DrugHub Transactions
The DrugHub marketplace exclusively accepts Monero (XMR), which uses ring signatures, stealth addresses, and RingCT to make transactions untraceable. Unlike Bitcoin, Monero protects both parties from blockchain analysis. When funding your account, always send XMR from an intermediate wallet rather than directly from an exchange. Use Feather Wallet which connects through Tor by default. The multisig escrow holds funds in a 2-of-3 arrangement, ensuring no single party can access escrowed funds.
Common DrugHub Verification Mistakes
Even security-conscious users make these errors when verifying marketplace links. Knowing what to watch for helps you avoid the most common pitfalls that lead to compromised accounts and stolen funds.
Trusting Visual Appearance Over Cryptographic Proof
Phishing sites replicate the DrugHub marketplace pixel-for-pixel, including colors, layout, and product listings. Some even proxy real data. Visual appearance proves nothing about authenticity. Only a valid PGP signature from the official signing key confirms a URL is genuine. Use Qubes OS or Tails for operating-system-level isolation when accessing the marketplace.
Importing PGP Keys from Unverified Sources
An attacker can create a counterfeit PGP key with the market team's name, sign a fake mirror list, and distribute both together. If you import that fake key, verification shows "Good signature" but the URLs are phishing mirrors. Always compare the fingerprint from your imported key against this page, Dark.fail, and the Dread subdread. Transfer verified key files using OnionShare over Tor to avoid interception.
Relying on a Single Verification Source
Checking a marketplace URL against only one source is insufficient. If that source is compromised, you cannot detect the manipulation. Cross-reference at least two independent sources: this official page, Dark.fail, and the Dread subdread. If a URL appears on all three with matching PGP signatures, it is legitimate. Privacy Guides recommends multi-source verification for all security operations.
Ignoring Expired or Revoked Keys
If the marketplace team rotates their signing key, old signatures become invalid for new mirror lists. Always read the full GnuPG output carefully, as it states whether a key is expired, revoked, or untrusted. If you see any warning other than "Good signature," do not trust the result. Check this page and the DrugHub wiki for key rotation announcements.
DrugHub Verification Frequently Asked Questions
Answers to common questions about verifying marketplace links, PGP key management, and staying safe when accessing the market through Tor.
DrugHub uses a 4096-bit RSA PGP key to sign all official mirror lists and announcements. The key is published on this page, the Dread subdread, and Dark.fail. Always cross-reference the fingerprint against at least two sources before using it for verification. The same key is used for PGP-based 2FA on the marketplace.
First-time setup including GnuPG installation and key import takes about ten minutes. After that, verifying a new mirror list takes under two minutes. Once the marketplace public key is in your keyring, each verification is a single terminal command.
A failed verification means the mirror list was modified or never signed by the official team. Do not use any URLs from it. Delete the files, obtain the list from a different source, and verify again. If failure persists across sources, check the market's Dread subdread for key rotation announcements.
You can cross-reference links against multiple sources like this page, Dark.fail, and Dread. If the same onion address appears on all three, it is very likely authentic. However, this is weaker than PGP verification, which provides mathematical proof. PGP remains the recommended method for confirming any marketplace mirror.
The primary sources are Dark.fail, the Dread subdread, the DrugHub Market main site, the DrugHub onion URL list, and the DrugHub access guide. Using at least two sources together with PGP verification gives you the highest confidence that a mirror URL is genuine.
If you have a verified URL bookmarked in Tor Browser, you do not need to re-verify every session. Re-verify when mirrors rotate, your bookmark stops working, or you get a URL from a new source. The anti-phishing canary displayed after login provides additional per-session confirmation you are on the real platform.
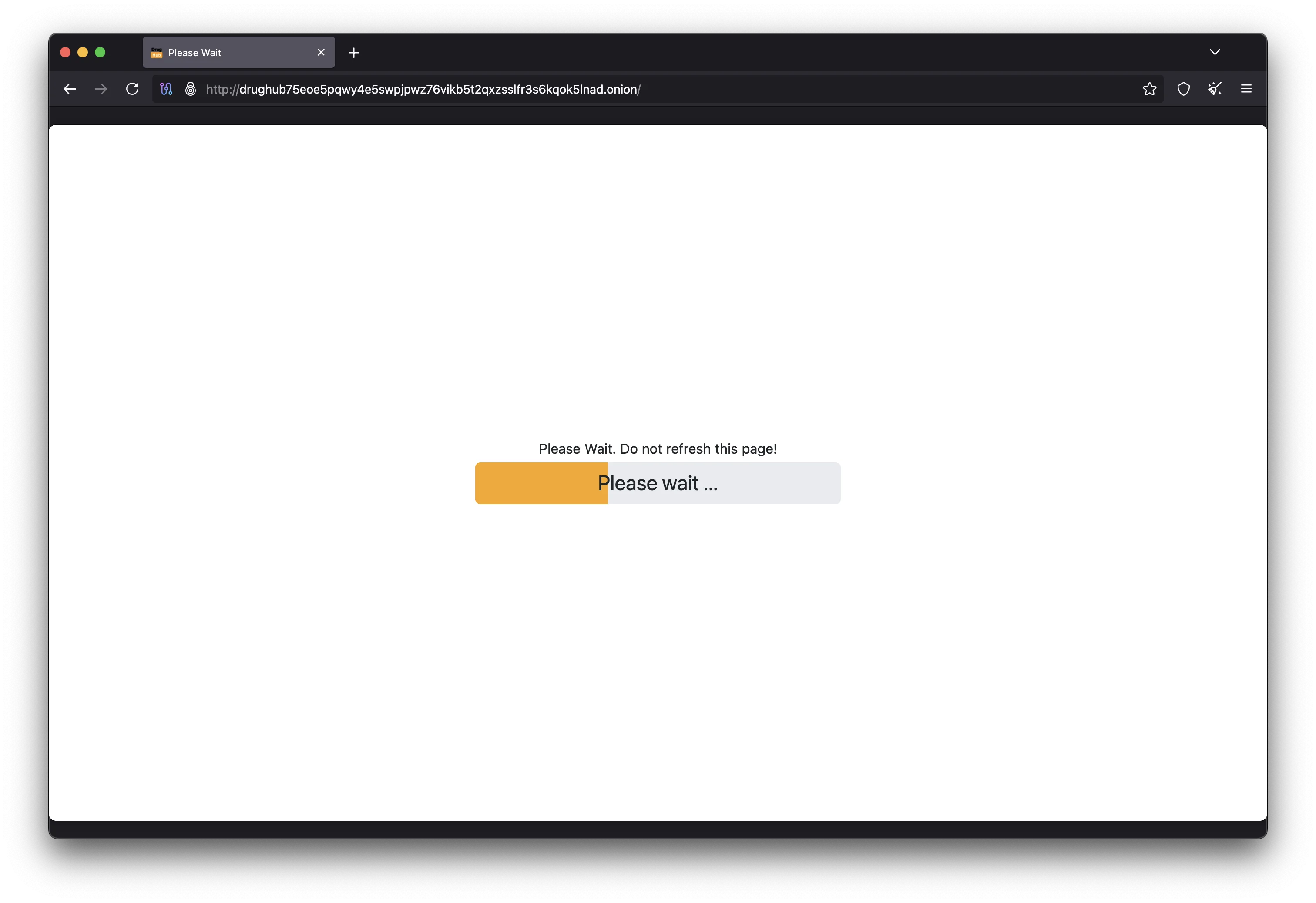
DrugHub operates as a Tor hidden service, so DNS-based attacks do not apply. The .onion address is a cryptographic identifier, not a DNS name. Traffic is encrypted at every relay hop. The END GAME anti-DDoS system filters malicious traffic at the application layer. Combined with PGP-signed mirror lists, these protections make the marketplace resistant to network-level attacks.
The onion address below has been verified with the official PGP key and is tested daily for availability. Copy it into your Tor Browser to access the marketplace securely.
drughub75eoe5pqwy4e5swpjpwz76vikb5t2qxzsslfr3s6kqok5lnad.onion
Open this address in Tor Browser only. Standard browsers cannot connect to .onion hidden service addresses. For the full list of backup mirrors, visit the DrugHub verified links page or return to the official homepage.
Verify Before You Connect to DrugHub
Always verify marketplace links with PGP signatures before entering your credentials. Visit our mirror page for the latest tested onion URLs or return to the official homepage for security guides and status updates.